Too often, information risk accountability isn’t at the right level due to poor alignment between security and business leaders. It’s time to transform the way we communicate risk to the business. When the security program struggles with an issue, bring the discussion to the people who can effect change. Bring it to the business leaders that own the risk, the policy, the resources, and the budget.
Key #2 for Cybersecurity-Business Alignment

In an effective risk culture, the business executive risk owners are well informed about risks and take accountability for them. They’re able to integrate risk considerations into managing value-producing business processes and strategies. They can express their risk tolerance (aka appetite) to technical and operational teams, and direct the risk treatment strategies at a high level. This is how most companies manage financial risk. They will be able to do the same with information risk when it is described for them in financial terms.
Why Isn’t the Risk Ownership Obvious?
Most organizations have strict financial rules, or policies, that control spending authority by the level of management in the organization. A Supervisor, Manager, Department Head, Division Head, VP, Chief Operating Officer all have (increasingly higher) budgets and expense approval limits.
These same organizations also have policies for risk acceptance. Many companies quantify financial and operational risk, formalize risk acceptance processes, and specify risk acceptance sign-off levels. They quantitatively specify sign-off levels just like expense limits or budgets. Quantitative financial risk models use tried and true techniques like Monte Carlo simulation.
However, most organizations still employ qualitative assessment methods for IT, cyber, or information risk. In other words, an information risk scenario might be rated as “high risk” because it was assessed as a “4” on a scale of 1 to 5 rather than having a dollar value placed on it (such as annual loss expectancy of $150 million and worst case loss estimate of $450 million).
I consider the lack of quantified information risk, or loss exposure data, one of the glaring flaws in our practice that creates the disconnect on risk accountability. And that is because without quantification information risk ownership becomes non-obvious.
How to Put Information Risk into Business Terms
What business leaders don’t understand, they may not be willing (or able) to take accountability for. I’m currently writing an ISACA Journal case study on a European company’s Factor Analysis of Information Risk (FAIR) program. Per the company’s risk team leader: “Before FAIR, more often than not information risk was rated too low when a financial value had to be assigned. This created difficulty with our company’s risk acceptance process which, by policy, required higher levels of sign off depending on the risk amount. IT department heads were accepting risks that materialized higher than estimated, and should have been signed off by the business owner. Also, the IT managers didn’t have the budget to mitigate those risks. In 2017, we experienced a large data breach.”
Until the Open Group standardized FAIR a few years ago, the security community lacked the ability to quantify risk in a consistent and defensible way. Today, however, Open FAIR incorporates Monte Carlo simulation well as calibrated estimation and other techniques that will bring information risk management into the 2020s.
Often just going through the FAIR decomposition process (without doing exhaustive analysis) has value. FAIR’s approach to risk decomposition becomes a structured forum for business and IT or security teams to work together on collecting data or refining scenario assumptions. Each participant in the process brings different subject matter expertise to the table. For example, security staff are more familiar with the threats, vulnerabilities, or controls that can determine the frequency of adverse events. But IT and business people have a better understanding of the operational and business impacts.
|
“The process of working through FAIR risk assessments is like IT Therapy.” — Recent Washington DC FAIR Institute Chapter meeting attendee. |
Quantitative FAIR Analysis Helps Us Account for Information Risk
With all the coverage of cyberattacks and vulnerabilities, there’s a sense of drowning in information risk, that cybersecurity is getting worse. But there’s no clear accounting of how bad it is, how we can fix it, how much that should cost, and what we should do today.
What if we could account for information risk? Imagine risk appearing on a business’s future- or forward-looking accounting forecast, as shown in the figure below. Much as forecasted operating assets and revenues comprise the “assets” side of the ledger, outflows from risks that could materialize into losses could join forecasted business expenses on the “liabilities” side.
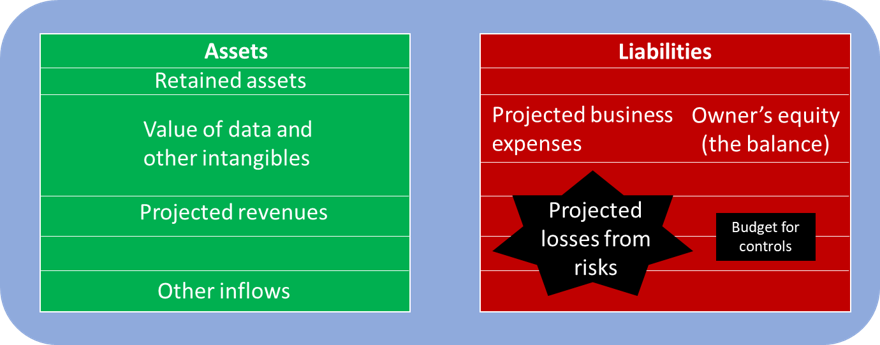
The concept of projected losses from risks is the subtext for the security program. What’s less well understood is that just as business executives are accountable for the financial bottom line, they’re also accountable for risk exposure. Business leaders – such as the CEO and lower-level line of business (LOB) leaders – are the “risk owners.” They must ensure that actual losses remain at a tolerable level, and to do that requires risk management.
This is the critical point. Cybersecurity-business alignment begins with accountability for risk as well as the roles and responsibilities for risk management. Quantitative risk management is a core competency for alignment.
Conclusion
Chapter 5 of my book – Rational Cybersecurity for Business – provides some guidance on how to “Manage Risk in the Language of Business.” It suggests ways to triage and prioritize risks, and to quantify the key risk scenarios in business terms such as the potential time and money impact of a breach against a new product launch or one of the business’s key customers.
The typical business doesn’t actually have a ledger like the conceptual one in the above figure. But many businesses do track risks at the enterprise level using a “risk map” or “risk register.” The risk map is a common tool used in enterprise risk management (ERM) to represent the top risks to the business on a graph showing their likelihood of occurring and potential impact. In my next post, I’ll talk about weaving information risk into the enterprise risk map.
Where does the information risk accountability sit in your organization? Have you tried quantified risk management, or found another good way to foster business risk owner accountability? Please comment below or Contact Me.
Related Reading
Keys to Cybersecurity-Business Alignment Post #1: Rational Cybersecurity at RSA: The Human Element
