Exciting News: I found the perfect publisher for Rational Cybersecurity for Business. Apress, a Springer Nature company, will be publishing my book in May 2020 through the ApressOpen program. This means the industry’s first comprehensive Security Leader’s Guide to Business Alignment will get the widest possible distribution. Perhaps you’ve heard this truism: Users can be your greatest asset or your greatest liability for security. That’s why it’s critical to give CISOs and security leaders just as much guidance on how to engage business stakeholders as we do on technical matters.
Tackling the Cybersecurity-Business Alignment Challenge
The general public expects organization’s security teams and the industry to protect them from cybercriminals and other threats, but sometimes we seem to be losing the battle. But what if we knew that cybersecurity’s plight is as much a leadership and organizational problem as it is a technical one? We’d want to get CISOs and other security leaders – the book’s primary audience – the guidance to align their security programs with the business and create optimal people, process, and technology solutions.
Great Open Source Security Publisher
The ApressOpen program assures that Rational Cybersecurity’s digital editions will be freely available and shareable. This brings the impeccable quality of a full service publishing operation together with open source distribution. Apress has already published many technical books using this model, including some other security titles. Starting with Rational Cybersecurity being available for open access, we can now open source the information flow throughout the industry on cybersecurity-business alignment.
My Rational Cybersecurity Journey
Why do this? In three decades of security research and consulting, I’ve seen way too many organizations with disengaged business stakeholders. Disengagement takes two basic forms:
- Management just doesn’t consider security to be a priority.
- Or, they’ve budgeted for security, hired staff, and deem it “handled.” They delude themselves into thinking they’ve put security first even if in practice it is routinely put way behind other priorities.
We see the second, insidious, form of disengagement even at highly regulated businesses. In some cases, business and security staff alike are afraid to do anything other than put an optimistic spin on security issues reported up the chain. In other cases CISOs burn out, flame out, move out, and leave the security program in tatters.
Misalignment between security and the business can start at the top or happen at the line of business (LOB), IT, development, or user level. It leads to what I call the Cybersecurity Deficit and has a corrosive effect on any security project it touches. And as organizations transform themselves into digital businesses they fall under increasing IT-related risk and regulation. Aligning cybersecurity and IT with business leaders and business processes is exponentially more important to digital businesses.
The good news is that we can put better information in the hands of CISOs and other security leaders on how to communicate more effectively with senior management and other levels of the business about each specific alignment issue. That will start to improve engagement and security program outcomes.
Organized to Emphasize Cybersecurity Business Alignment
Cybersecurity is a vast topic, and businesses have different cultures, drivers, missions, models, and products or services. Facing a general problem statement of “How should security align with business?” one could easily get lost in minutiae or platitudes.
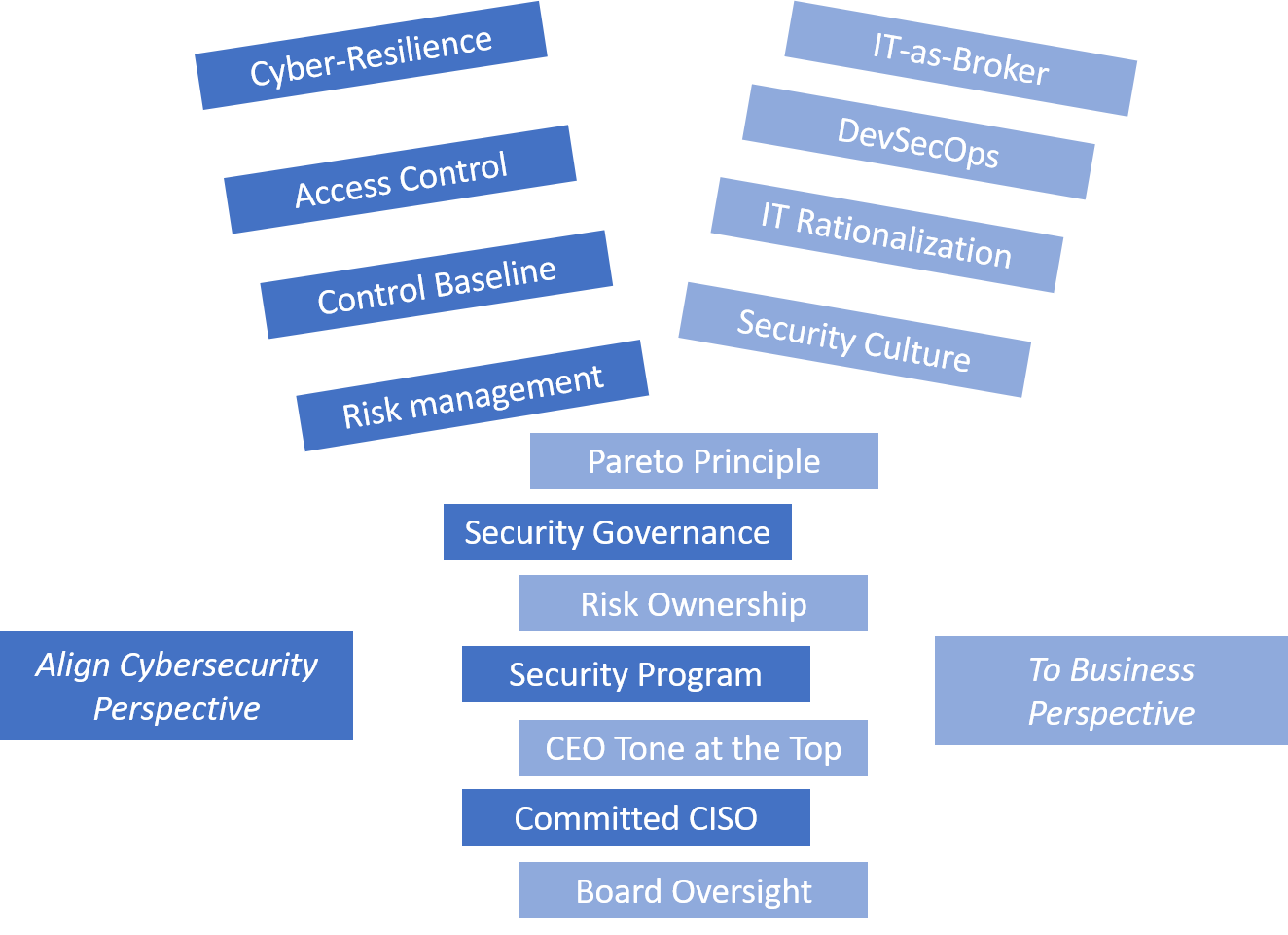
It’s can also be hard to stay focused on alignment while trying to explain the many good practices for security people, process, and technologies. Therefore, as I wrote in my Q3 and Q4 updates, the book applies the 80-20 rule (aka Pareto Principle) to cybersecurity as its organizing framework.
The Cybersecurity Pareto Principle
How can security leaders get 80% of the benefit by doing 20% of the work?
Rational Cybersecurity for Business covers six priority focus areas shown in the figure below to maximize cybersecurity program effectiveness.

With at least one chapter for each of the Cybersecurity Pareto Priorities, Rational Cybersecurity will be the only comprehensive field guide for CISOs and security leaders on exactly how to align with the business from the Board of Directors and top Executives down to LOB leaders, corporate administration, compliance, IT, development, managers, and staff. To bring the material home to the target audience, it includes many security stories related by CISOs or other business and security leaders during over 60 interviews.
Still on the Road to 100 Cybersecurity Interviews
More than sixty interviews so far have provided great insights to this book. We still have a month or two before the publisher declares a “freeze” on any substantive changes. Even then, I’ll keep going to 100 interviews (and beyond?) so as to continue a cybersecurity-business alignment conversation with the industry. If you’re a security or business leader and would like to be interviewed for the book, or if you have ideas on how to get the cybersecurity-business alignment message out via additional media opportunities, let’s talk.
Keys to Cybersecurity-Business Alignment
I’m serious about wanting to increase the information flow, and am starting now with a weekly Keys to Cybersecurity-Business Alignment Blog Series. These posts will leverage more than 50 specific keys to alignment within the book’s own narrative. I’ll expand on each one as best as I can in each post, and hope that all you security leaders out there will help me promote them on social media.
